Connect to Active Directory
The following video and page will cover how to connect to Active Directory when using Data Synchronisation Studio. The video specifically covers connecting to the user object in Active Directory.
The Active Directory provider in Data Sync is a read-write connector for Active Directory User, Contact, Group, and Computer objects. The connector also supports incremental sync.
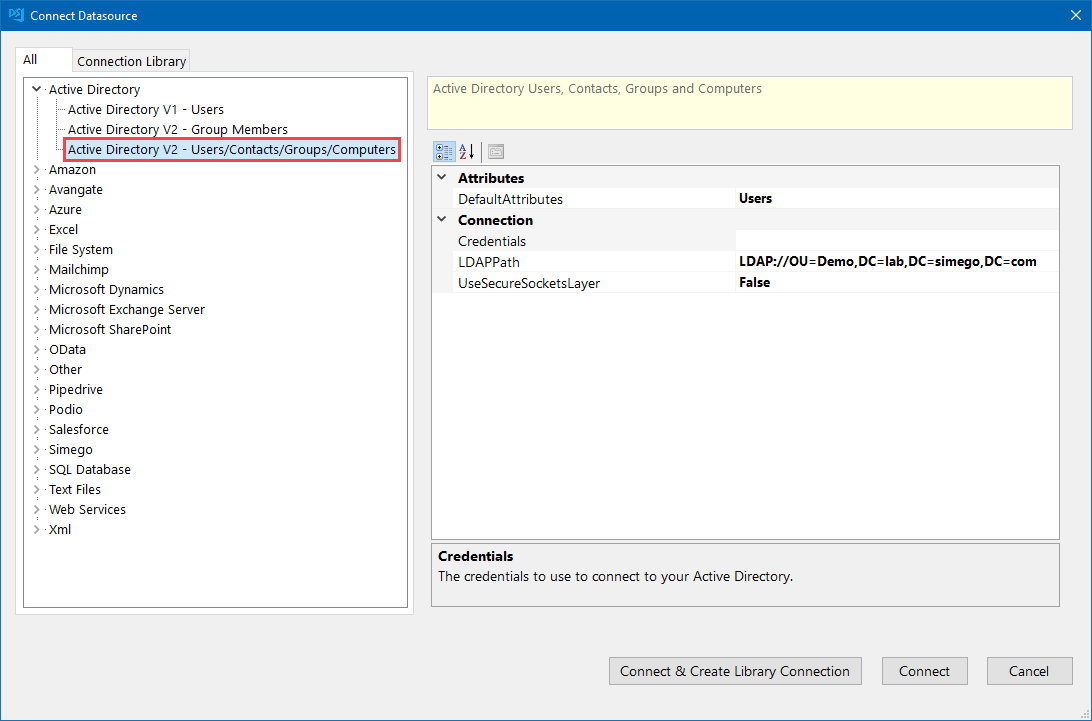
When you click onto the Active Directory section in the connection window you will have a few options to choose from.
Active Directory V1- Userswill connect to AD using the old connector. This is lacking the new features that will be mentioned below. You can see the documentation for this connector here.Active Directory V2- Group Membersis the connector you can use to connect and return groups and the users that are members of those groups.Active Directory V2- Users/Contacts/Groups/Computersis the connector you can use to connect to users, groups and computers. It is likely that this is the connector you will use most frequently to connect to Active Directory. This will be the connector discussed in the sections below.
You can find the general connection details below and further details for each connector and additional guidance are available in the links to the left of this page.
To connect to Active Directory you need to enter your Credentials and LDAP Path at a minimum.
Add your Credentials
Your credentials are the Windows Credentials you use to connect to AD. If you leave these blank, then the current process/user credentials are used.
To add your credentials, click onto the ellipsis (...) to open the credential window.
Enter the LDAP Path to your OU
You can enter in either the full LDAP Path or simply the server name/domain controller name.
If you want to use just the server name/domain controller name your connection would look similar to: LDAP://dc01
Otherwise examples of full LDAP Paths are:
You can connect to your global OU by omitting any OU's from the path, note that you will need your domain controller name to be listed:
LDAP://dc01/dc=demo,dc=simego,dc=comYou can connect to a specific OU by adding the OU to the path, note that you will need your domain controller name to be listed:
LDAP://dc01/OU=Test,DC=demo,DC=simego,DC=com
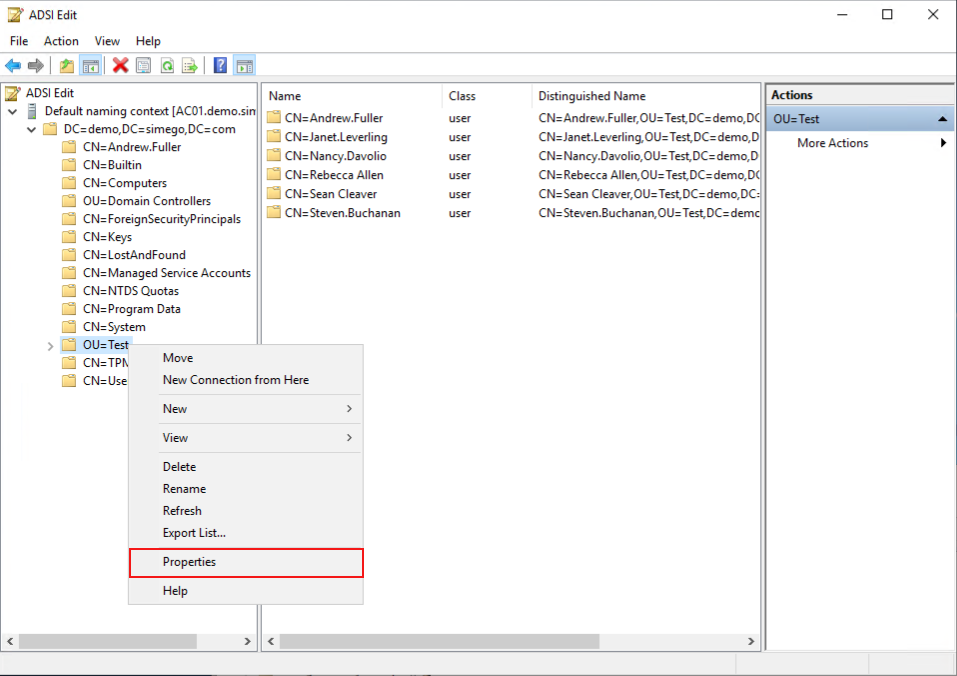
If you are struggling to find your LDAP Path you can use ADSI Edit to help you.
Find your LDAP Path
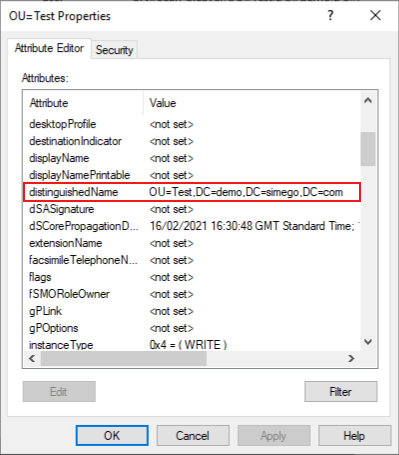
In ADSI Edit locate your OU, right click and select Properties from the list.
Then find the distinguished name attribute in the list and this will give you the LDAP Path to that OU.
UseSecureSocketsLayer
If your AD has SSL enabled you can connect using SSL by changing this to True by selecting the value from the drop down list.
Edit the Connection Properties (Optional)
Add any additional Attributes
Use this to add additional attributes that are not listed by default. You can learn more about this here.
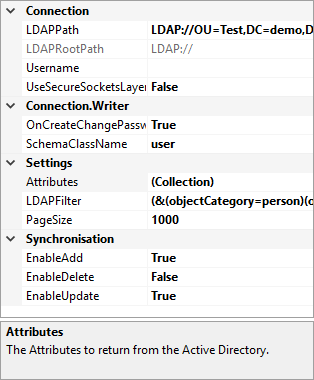
Apply an LDAP Filter
You can apply an LDAP filter to your connection to limit the results on the server side.
The default filter is set as (&(objectCategory=person)(objectclass=user)) for the User connection.
You can find the Microsoft LDAP Filter Syntax here.
You can also find more details on using the LDAP Filter here.
Group Filter
You can use an LDAP Filter to limit the results returned from Active Directory.
The LDAP filter below is an example filter that returns users that are members of the CRM Team Users Active Directory group
(&(objectClass=User)(memberOf=CN=CRM Team Users,CN=Users,DC=corp,DC=litware,DC=inc))
Edit the PageSize
The number of Active Directory objects to return in each query request default 1000.
Specify the object type to use when creating new object with SchemaClassName
This is used when creating Active Directory objects. It specifies the type of object to create either User, Contact, Group, or Computer.
Require users to change their password using OnCreateChangePasswordNextLogon
If a user account is created and a password is set then set the flag in AD to require the user to change their password at the next logon.
By default this is set to True.
